...
Communication line category: OPC UA Client
Host address: OPC UA server address. You may set the name according to UNC convention (e.g. "\\server" or "server", DNS names (e.g. "domain.com", "example.company.com") or IP address ("196.54.23.113"). In the case of redundant systems, multiple names/addresses separated by commas or semicolons can be entered.
The usage of the alternative path (the second or following name/address) is signalized by the FLB flag and a combination of FLN, FLO, FLP flags in the station value.
TCP port: TCP port of OPC UA server (e.g. 4840).
EndpointUrl: Endpoint address (e.g. opc.tcp://localhost:4840)
Encoding type: Type of encoding that is used for data exchange (currently only Binary encoding is supported).
...
| Parameter name | Meaning | Unit | Default value | ||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Type of used client (driver for OPC UA communication):
| Default Secure | Default | ||||||||
| Session text identifier. Session identifier should be unique within the client instance, making it possible to search problems faster in the client or server logs. | String | Kom process | ||||||||
| The channel must be reopened before this time limit elapses. If the time is exceeded, the channel will be closed and unable to change data. | hh:mm:ss | 01:00:00 | ||||||||
| Any message should be changed between client and server before this time limit elapses. If it is not sent, the sources within the session that are kept on the server are released. The primary work of this parameter is to remove the sessions that became inactive because of some unexpected reason. | mm:ss | 01:00 | ||||||||
| Type of authentication used with the OPC UA server. Supported types are:
| Anonymous / Username | Anonymous | ||||||||
| If Authentication type = Username, then user name used in the authentication. If Authentication type = Certificate, then path to user certificate (e.g. D:\user_cert.der). | ||||||||||
| If Authentication type = Username, then password used in the authentication. If Authentication type = Certificate, then path to user private key (e.g. D:\user_private_key.pem). | ||||||||||
| Security policy (only for Client Type = Secure; for Client Type = Default a security policy None is used):
| None Basic128Rsa15 Basic256 Basic256Sha256 Aes128Sha256RsaOaep Aes256Sha256RsaPss | None | ||||||||
| A mode of message security in OPC UA communication (only for Client Type = Secure; for Client Type = Default a mode of message security None is used):
| None Sign Sign & Encrypt | None | ||||||||
| Identifier of preferred Security Policy (only for Client Type = Default for password encryption). If the OPC UA offers several security policies, it is possible to select a specific one according to the identifier sent by the OPC server (the identifier can be found from the logs). Examples of an identifier (text form is in parentheses): PolicyId: 30 (0) PolicyId: 31 (1) PolicyId: 75 73 65 72 6E 61 6D 65 5F 62 61 73 69 63 31 32 38 52 73 61 31 35 (username_basic128Rsa15) PolicyId: 75 73 65 72 6E 61 6D 65 5F 62 61 73 69 63 32 35 36 53 68 61 32 35 36 (username_basic256Sha256) | - | - | ||||||||
| Waiting after the connection Waiting after the connection is broken before the connection is re-established. | mm:ss.mss | 00:10.000 | ||||||||
| Waiting after an unsuccessful connection attempt. | mm:ss.mss | 00:02.000 | ||||||||
| It changes the number of information about communication. We recommend enabling the Extended/Full modes only when detecting the problems and debugging the communication. The "Full + Trace (Secure only)" mode is valid only for Client Type = Secure. | Normal/Extended/Full/ Full + Trace (Secure only) | Normal | ||||||||
| The parameter defines the thread(s) that will send the debug info about the communication. | Receiving/Sending/Others treads/All threads | All threads |
...
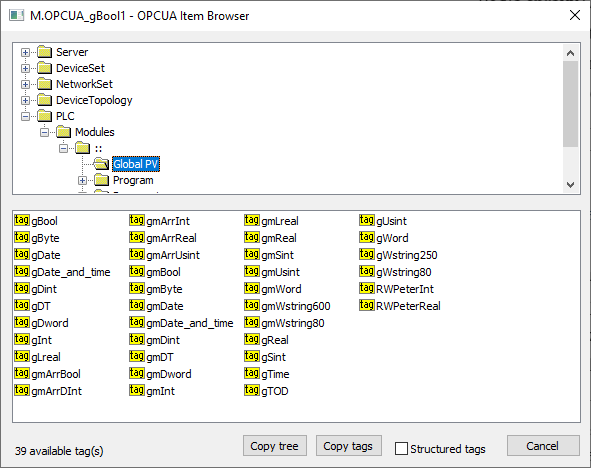
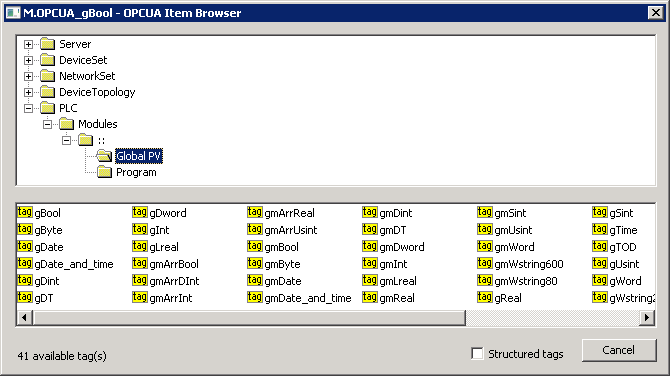
Note: In versions from 17th December 2018 and newer, the recycling of browser dialog has been implemented. If the dialog is closed by the Close button or after selecting a tag, it is actually only hidden and it is available for browsing by another I/O tag within the same station so that the tree structure of the browsed objects is preserved. Clicking on the close icon at the top right corner will cause the dialog to be really closed.
"Copy tags" button or a keyboard shortcut Ctrl+C copies the names of tags in a selected branch into the tree structure of the browsed objects is preserved. Clicking on the close icon at the top right corner will cause the dialog to be really closed.Windows clipboard. All tags will be copied unless a specific tag is selected.
"Copy tree" button or a keyboard shortcut Ctrl+Shift+C copies the names of tags and their addresses in all browsed branches into the Windows clipboard.
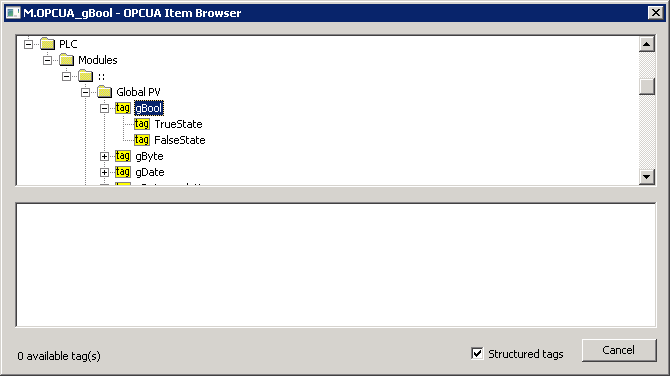
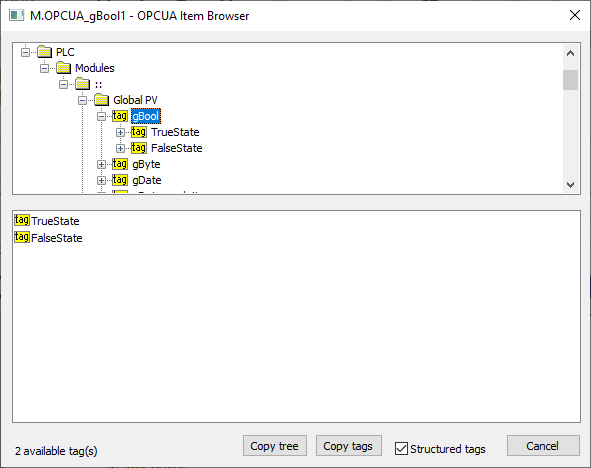
Checking the "Structured tags" option causes the variables (tags) to appear in the tree structure in addition to the objects, and the KOM process also attempts to read their descendants. This is useful for browsing OPC UA servers that support structured tags. You can also insert a tag into the address dialog window of the I/O tag by double-clicking the tag name in the tree structure.
| Kotva | ||||
|---|---|---|---|---|
|
...